Cybercriminals are no longer just faking legitimacy. They are now using Google’s infrastructure to take over thousands of Facebook accounts.
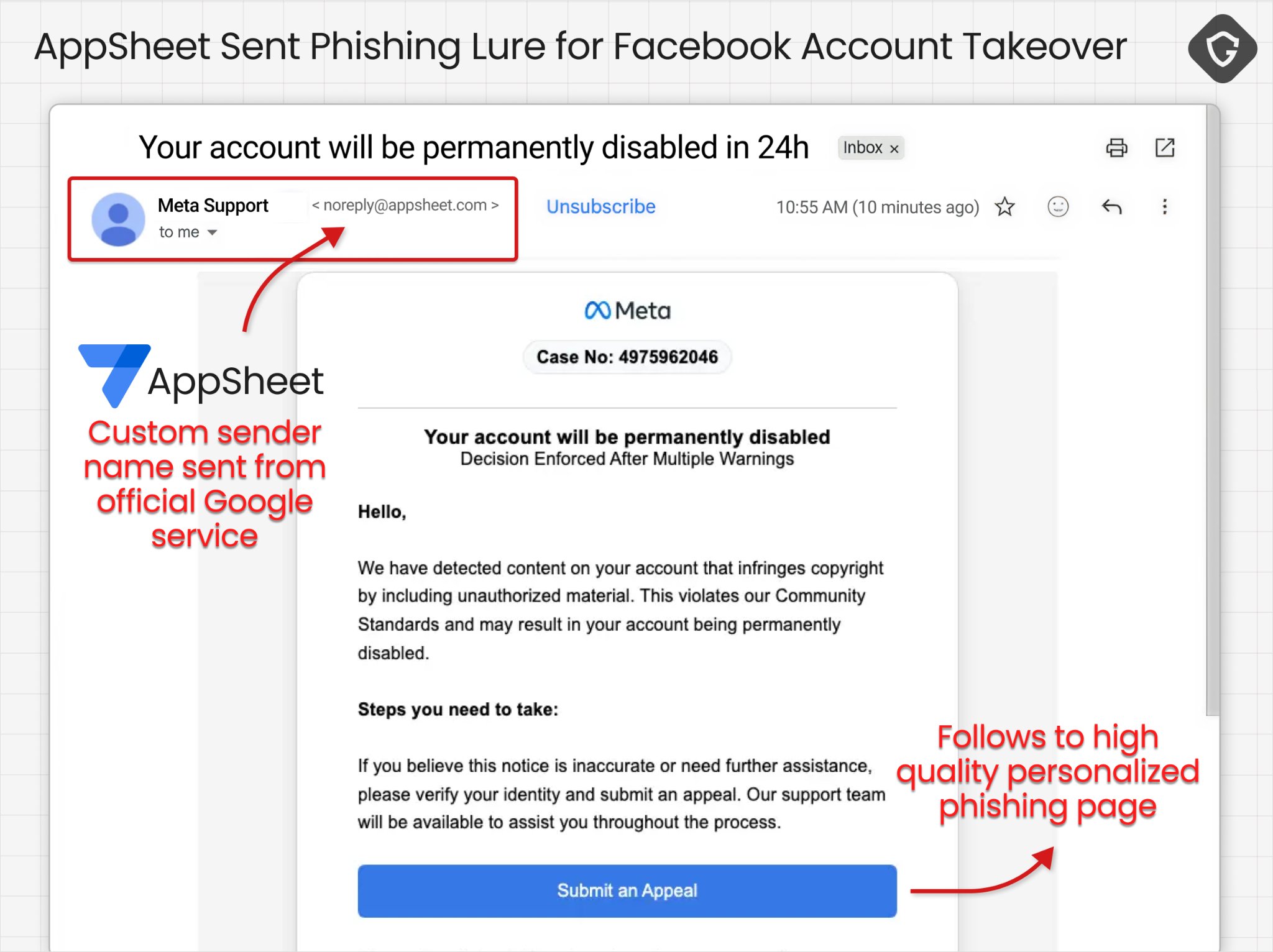
Researchers have uncovered a campaign that abuses Google’s AppSheet to send phishing emails that appear legitimate and slip through standard authentication protocols. That allows the messages to bypass scam alerts and land directly in the targets’ inboxes.
The campaign is linked to a Vietnam-based operator that has already compromised 30,000 accounts with stolen access feeding into its organized resale and fraud networks.
By impersonating Meta support, they send urgent claims about account violations, shutdowns, or, sometimes, recruitment opportunities from other platforms, directing victims to fake pages designed to compromise their accounts.
The campaign indicates a growing shift in how phishing attacks are conducted. Attackers now rely on trusted platforms instead of imitating them. By using legitimate tools and platforms, they increase their success rates while lowering suspicion from both users and security systems.
Security researcher Shaked Chen calls this approach a “phishing relay,” where trusted systems act as user-facing intermediaries for malicious campaigns.
In this case, the attacker abused Google AppSheet’s built-in email capabilities. AppSheet is a free no-code platform that allows users to create apps. Users can connect data sources from Google services such as Drive and Sheets, define automation triggers, enabling them to send email notifications without needing software engineering expertise.
While its functionality is designed for business efficiency, an unintended consequence is that it creates a delivery channel that, when exploited for malicious purposes, becomes highly dangerous. Emails sent through AppSheet are routed via Google’s infrastructure, which provides valid authentication signals and a level of trust that typical phishing messages lack.
Attackers exploited that trust by leveraging the platform to send convincing phishing messages to Facebook business accounts.
In the observed attacks, the messages were delivered from “[email protected],” and because they originated from Google’s infrastructure, they passed undetected. A more interesting and subtle factor at play here was that the email sender had a verification mark, a very visible sign that many email users use to quickly judge an email’s legitimacy.
The research report says the emails focused on alleged Meta copyright violations, warning of account shutdowns and pending verification reviews, and directing recipients to a phishing link embedded in a call-to-action button.
A distinct strategy within the same campaign impersonated recruiters from companies like Apple, Coca-Cola, Pinterest, Adobe, Meta, and its subsidiaries, using enticing offers to get targets on calls hosted on attacker-controlled sites.
Investigations also found that these attackers rely on mainstream cloud services like Google Drive, Netlify, and Vercel to host their bogus sites or malware documents.
Once victims submit their details, the data is automatically routed through attacker-controlled Telegram bot channels, where operators validate it, enabling them to quickly take over the accounts.
The chain of attacks suggests it’s run by a coordinated attack group, with a repeatable pipeline for account compromise.
Attack source, scope, and targets
The campaign, known as AccountDumpling, has been traced back to Vietnamese-linked operators offering digital marketing services as a public-facing business through the website phamtaitan.vn.
The group is said to be actively targeting Facebook business and advertiser accounts, likely because these accounts have access to financial and personally identifiable information (PII). About 30,000 of these accounts have been compromised so far, in what Chen says is an ongoing attack.
The geographic impact is quite large, with victims spread across 50 countries. The top countries include the US (most targeted), Italy, Canada, the Philippines, India, Spain, Australia, the UK, Brazil, and Mexico.
Compromising the accounts results in immediate monetization across several channels. When they are not running fraudulent ads, they are executing scams using hijacked pages or even selling access to accounts on dark marketplaces.
In some of the observed cases, the same attackers sell account recovery services to their victims.
Must-read security coverage
Preventive measures to stay safe
In almost every phishing case, the underlying access mechanism remains the same: it relies on human weaknesses. While this particular campaign borrows trust from reputable platforms, it leaves visible clues that anyone with a careful look can easily see.
- Double sign-in: It is unlikely that Facebook will request that you sign in again if you are already signed into your account. This little distinction matters in attacks like this that require you to sign in again.
- Check the sender’s email addresses: Although hackers often try to create an email address that looks similar to the real thing, in this case, their choice of email address is to bypass email security, which gives careful targets an edge. If the sender’s address does not match the platform they claim to represent, it is usually a big flag.
- Check in-app alerts: If an email claims there’s a critical issue with your account, Facebook should also send the same message via in-app notification. Confirm it inside the app before taking any action.
- Beware of random offers: If you receive a job offer you never applied for, there is a high chance it is a phishing attempt.
For security teams, keeping your organization safe requires proactive threat intelligence. Guardio has listed the indicators of compromise (IOCs) from this campaign, which can be accessed from the report page.
Also read: Several of the biggest cyber attacks of 2026 show how stolen credentials, exposed systems, and trusted infrastructure remain recurring security risks.
Read the full article here