A passkey is a specific authentication method that can be used as commonly as a password but to provide additional security. Passkeys differ from passwords as they combine private and public cryptographic keys to authenticate users, whereas a password relies on a specific number of characters.
According to Google, the most immediate benefits of passkeys are that they’re phishing-resistant and spare people the headache of remembering numbers and special characters in passwords.
As passwordless authentication continues to evolve — in response to phishing-related risks — consider using passkeys to implement an added layer of security to protect your online accounts and data.
This article will define passkey technology, explore how it works, and discuss the added security benefits of using a passkey.
1
NordPass
Employees per Company Size
Micro (0-49), Small (50-249), Medium (250-999), Large (1,000-4,999), Enterprise (5,000+)
Micro (0-49 Employees), Medium (250-999 Employees), Enterprise (5,000+ Employees), Large (1,000-4,999 Employees), Small (50-249 Employees)
Micro, Medium, Enterprise, Large, Small
Features
Activity Log, Business Admin Panel for user management, Company-wide settings, and more
2
Dashlane
Employees per Company Size
Micro (0-49), Small (50-249), Medium (250-999), Large (1,000-4,999), Enterprise (5,000+)
Micro (0-49 Employees), Medium (250-999 Employees), Enterprise (5,000+ Employees), Large (1,000-4,999 Employees), Small (50-249 Employees)
Micro, Medium, Enterprise, Large, Small
Features
Automated Provisioning
3
Scalefusion Single Sign-On
Employees per Company Size
Micro (0-49), Small (50-249), Medium (250-999), Large (1,000-4,999), Enterprise (5,000+)
Any Company Size
Any Company Size
Features
Access Management, Compliance Management, Credential Management, and more
What is a passkey?
A passkey refers to a code or a series of characters used to gain access to a secured system, device, network, or service. Passkeys are often used in conjunction with usernames or user IDs to create two-factor authentication.
SEE: How to Create an Effective Cybersecurity Awareness Program (TechRepublic Premium)
After you’ve established a passkey, all you need to do is log in to complete the authentication process, typically using biometric data such as a fingerprint or facial recognition. For those who utilize a passkey, logging in becomes a simple, nearly automatic process; for malicious actors, it becomes nearly impossible.
The implementation of passkeys is highly adaptable since they may be configured to be cloud-synced or hardware-bound, contingent on the user’s choices regarding the particular application, service, or device.
How do passkeys work?
When logging in for the first time, a user who wants to access an app or website with passkey technology — such as NordPass — will be asked to generate an original passkey. This passkey, which will be required for authentication in the future, can be accessed using either biometrics or personal PINs based on the user’s selection and the capabilities of their preferred device.
Figure A
During this stage, two mathematically linked cryptographic keys are generated: a public key that stays with the website, service, or application but is connected to the account, and a private key that stays on the user’s hardware or cloud account.
How do you sign in with a passkey instead of a password?
Passkey authentication is done in the background, making login on the user’s end seamless — with just the click of a button.
Figure B
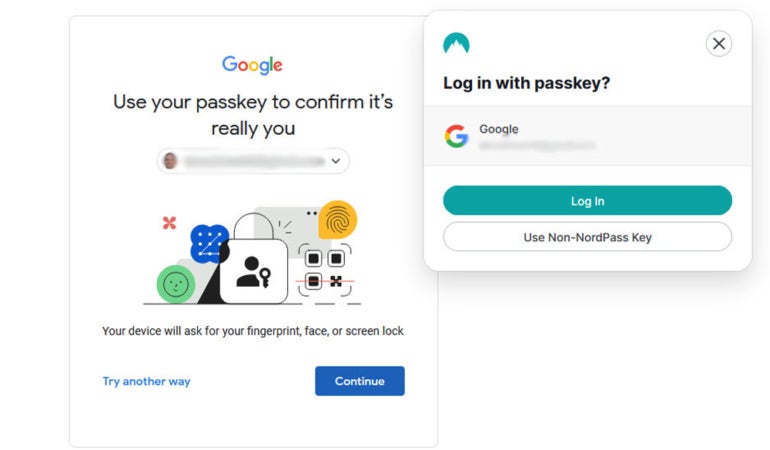
The service or application will send a randomly generated “challenge” to the user’s device during logins, which the user must react to by signing in with the private key.
SEE: Passkey Adoption Is Accelerating in APAC — Except for Australia (TechRepublic)
The app or website can confirm the legitimacy of the private key by utilizing the corresponding public key to confirm the response. Access is allowed, and authentication is validated if the user’s verified signature attached to the challenge’s response agrees with the original randomly generated challenge; if not, access is denied.
How are passkeys different from passwords?
The most critical differences between passkeys and passwords include:
- Passwords can be illicitly obtained through brute-force hacking, social engineering, and data breaches, whereas passkeys are more difficult (though not impossible) to steal. Hackers would need to physically steal your device or breach your cloud account and guess your PIN or find a way to bypass your biometric authenticator.
- Secure password usage requires users to generate and remember many complex credentials or employ a password manager, which has its own challenges and risks. Passkeys automatically authenticate users with their device’s unlock mechanisms, making them much simpler and more convenient to use.
- Passwords can be used across any device without any additional setup, but passkeys are usually bound to specific hardware. A cloud-based passkey solution may work across multiple devices, but users should be aware that their private keys will be stored on someone else’s servers instead of locally.
What are the benefits of using a passkey?
- Unique logins: A password is reused every time you log in to a particular account, which means any malicious actor who gets their hands on it will have unfettered access. Passkeys, on the other hand, use cryptographic key pair technology to create unique authentication credentials for every login, giving hackers nothing to “guess” or steal. Passkeys are resistant to brute force attacks and social engineering methods like phishing, plus they can’t be exposed in a data breach.
- Added security layer: Passkeys use your device’s authenticator, such as a biometric login or PIN code, as a sort of built-in 2FA that protects your account. Whether your private key is stored locally on your device or in the cloud, a would-be hacker would need to authenticate with your device before gaining access to it and compromising your account.
- User convenience: Passkeys don’t need to be memorized or periodically changed, and logging in with them requires a single button press, providing a much more streamlined experience than passwords. And, as I just mentioned, they include 2FA to better protect accounts, but they don’t require users to provide secondary authentication for each individual login — once you’ve logged into your device, that authentication is applied to every account you access that session.
What devices are compatible with passkeys?
Many devices from the most popular tech manufacturers are compatible with passkeys. Passkey technology was developed according to W3C and FIDO Alliance standards to aid in compatibility, and the big three device manufacturers (Apple, Google, and Microsoft), as well as all major web browsers, already support it.
Can passkeys be shared?
The implementation of passkey technology is still developing, but some companies have mentioned the potential for credential sharing amongst users — as long as the actual passkeys are kept safe in the cloud and out of the hands of potential hackers. Since sharing account access with family, friends, and coworkers is a very simple and quick process, this feature may improve the overall user experience. However, it is still unclear how this function can be securely managed in a business setting.
SEE: How to Use Google’s Titan Security Keys With Passkey Support (TechRepublic)
Another crucial factor to consider is whether businesses should become even more dependent on cloud providers and give up even more ownership and control over credential management, given that a breach of those parties’ data would, without a doubt, have disastrous consequences.
Hardware-bound passkeys, as opposed to cloud-based passkeys, are stored on security keys, physical hardware authenticators, or specialized hardware integrated into laptops and desktops. This means that the passkey is neither transferable nor duplicated. Hardware-bound passkeys can be an alternative for organizations wanting to prevent employees from copying or sharing keys across devices.
Are passkeys more secure than passwords?
Generally speaking, passkeys are more secure than passwords. However, their security depends on various factors, including the strength of the cryptographic methods used to encrypt public and private keys, the security of the device’s authenticator, and the trustworthiness of the passkey solution provider.
SEE: Nearly 10 Billion Passwords Leaked in Biggest Compilation of All Time (TechRepublic)
Users can take steps to make passkeys more secure, however. For example, passkeys use your device credentials as a second form of authentication, so using biometric login instead of a PIN can boost the security of your private key. Minimizing cookie collection and periodically clearing cached credentials are also good practices for improving overall web security. It’s also critical to complement passkeys with other security tools and controls, such as encrypted hard drives, device malware protection, and firewalls.
Can a passkey be hacked?
Yes, passkeys can be hacked, but it’s much more difficult than stealing a password. As I’ve described above, passkeys are protected by multiple layers of security, including local device authentication and strong encryption. Simply acquiring the private key is not enough because, even with cloud-based passkey solutions, you need to authenticate with the local device before you can access any online accounts.
Will passkeys replace passwords and password managers?
In my opinion, passkeys will eventually replace passwords and password managers, though the transition is currently still in the beginning phases. As passkey technology improves and more businesses adopt it, we’ll likely see passwords phase out even amongst home users.
What is the future of passkeys in technology?
Right now, most of the innovations in passkey technology are — correctly, in my opinion — focused on features, which are more convenient for developers and businesses to use in the hopes of driving adoption.
For example, right now, passkeys created in one ecosystem don’t easily work with others. So, if a user creates a passkey using their iPhone, it’s difficult, if not impossible, to use the same passkey on a Windows laptop or to transfer all of their passkeys from one environment to another.
This limitation, however, only really applies to the environment-native passkey tools that come with newer Apple, Windows, and Android devices. As more third-party passkey providers enter the market, the standard is beginning to shift toward cross-platform support and easier portability to improve the customer experience.
Read the full article here